- Témaindító
- #1
- Csatlakozás
- 2023.05.28.
- Üzenetek
- 23,223
- Reakció pontszám
- 528
- Díjak
- 6
- Kor
- 33
File size: 3 MB
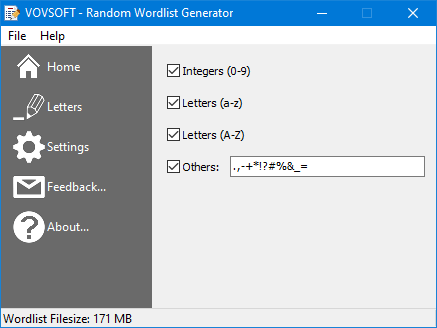
Random word lists are widely used for vulnerability assessment and penetration testing applications. You can utilize the lists in order to test brute force attacks. A brute force attack is an attempt to utilize the power of computers to match a credential, such as a password. Such an attack involves the automated spraying of all possible character combinations and lengths into a password field until a match is made.
Screen :
What's New
official site does not provide any info about changes in this version.
HOMEPAGE
Code:
⚠
A kód megtekintéséhez jelentkezz be.
Please log in to view the code.
Code:
⚠
A kód megtekintéséhez jelentkezz be.
Please log in to view the code.
